I am no fan of conspiracy theories and I usually dismiss them when it comes to aircraft accidents, or in this case, missing aircraft. However, as we approach the 1 year mark for the MH370 case, no trace of the aircraft has ever surfaced and while we wait for the ongoing search to continue and the lack of new available evidence, perhaps it is time to, reluctantly, take a look at these.
My viewpoint on MH370 is simple: if the aircraft went south, I don’t buy the view that this was a hijack or other forms of hostile takeover. The theory relies too much on damning the Captain who was a known sympathizer of Malaysia’s opposition. The circumstantial evidence were just too convenient. The so-called satcom logon and ping at 1825, in my opinion, invalidates this theory. There is little sense for someone to switch off the satcom and then switch it back on, if someone wants to disappear into the middle of the ocean. This was where I left MH370 last year.
Me, Jeff, TV Cameras, MH370 and “Crypto-Investigations”

I didn’t think much of the other conspiracy theories, but then after the Indonesia Air Asia QZ8501 accident, I began to be in contact with the so-called “Independent Group” (IG), a group of independent experts in what I call “crypto-investigators” due to their amount of work on MH370. One of their members was Jeff Wise, who was the expert who often appeared on CNN’s coverage on MH370. Through the lack of evidence in the initial stages of QZ8501, I began to communicate with Jeff Wise and the rest of the IG. It was then that I began to realize the level expertise that did the “crypto-investigation” into MH370, and inevitably, I too joined some of the discussions.
The similarities between me and Jeff is merely the fact that while was largely the remaining expert on MH370 for CNN, I was largely the remaining expert on MH370 for Agence France Presse (AFP), throughout the first month of the debacle. From a global list of 600 aviation expert (to which I rank very far down the list), by the time the satcom issue came out, I was virtually the last guy that can talk about the aircraft satcom and aircraft piloting at the same time, that was available to AFP. This is probably where the mutual respect between me and Jeff came from (which was boosted by our discussions on QZ8501).
While Jeff said he “was on-air up to six times a day as part of its nonstop MH370 coverage” and he “was spending 18 hours a day doing six minutes of talking”, which went on for a month with some variety to the “rhythm of perpetual chatter”, I spent about a month doing various interviews and did my “six minutes of talking” on international media and various 45 minute appeances on local media. 9 months later, the situation turned around with QZ8501, where Jeff did what I did for MH370, and I ended up not spending a day without seeing a camera for 3 weeks, and probably became the most Indonesian in the world aside from celebrities and politicans, with a record 5 hours of airtime on a single day feeding the perpetual chatter at one or up to 4 TV stations a day… filling up the “breaking news” during the news-less end of year season. It’s therefore easy to understand why I understand Jeff in a way.
But I can’t deny that I was shocked to see what Jeff wrote on February 23… It seemed that Jeff yielded to the conspiracy theories at his site and the New York Magazine.
My jaw dropped and , I thought, “Oh no… Jeff lost it!” However, the respect I had for Jeff got me to read the articles.
In true crypto-investigation style, the conspiracy was, while outlandish, set up in a way that shows it had a systematic flow to it. Of all the conspiracies theories I’ve seen appear on MH370, this is the best one so far in my opinion… mainly because Jeff remains skeptical to his own conspiracy theory.
I remember that saturday 14th March 2014 when I was running from the house to Jakarta’s Al-Jazeera studio for a 2 minute appearance regarding MH370 (after some repetitive rescheduling on their part), and immediately after my appearance, I went to Jakarta’s AFP office for my appointment with my friend and journalist there, Angela Dewan (who has since taken up another post elsewhere), where we watched Prime Minister Najib’s announcement that the airplane was detected to be “alive” until around 8:20 am the next day.
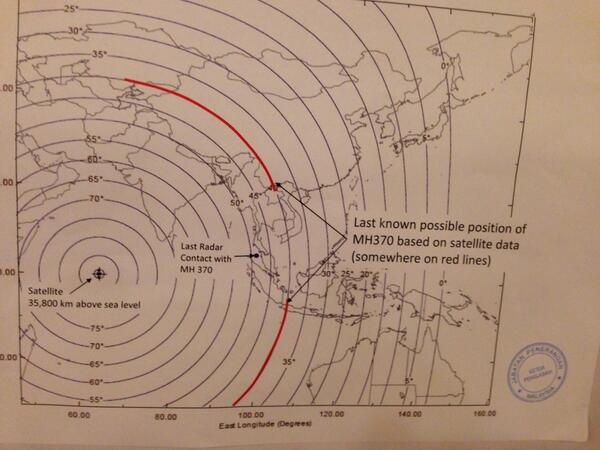
One question Angela asked in our long conversation that day that I remember to this day, “if the airplane did go north, where would it end up?” Ironically, the destination that immediately came up in my head was, “Baikonur… it’s pretty remote.” However, neither me nor Angela, nor any other journalists that discussed this with me ever thought much of the northern path because if it it did, “how did it get through all that” was my quoted answer regarding that possibility, and that it wasn’t long before the BFO analysis concluded the aircraft went south. The northern path was then buried far down below in my list of priorities.
So what was interesting in Jeff’s “crazy theory”?
For someone like Jeff to come up with such a theory requires a lot of bravery, and needs to be looked at even for just a little bit, at least to freshen our minds. I emailed him immediately after reading the New York Magazine article, telling him that someone in the past mentioned something similar to his theory. The first sentence in his reply was:
“Thanks very much, it means a lot coming from you.”
This tells me, we’re all just so fed up of being stuck in the black hole of information with no new updates for the last 6 months, and that to fill our time, maybe it’s time to look at some alternatives, as ridiculous as they may be.
The purpose of such exercise is to keep our minds sharp, and our imagination tested, which is very important in this “crypto-investigation”.
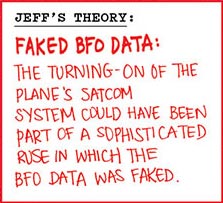
Whilst the BTO (pings) are not doubted whatsoever, the Burst Frequency Offset (BFO) which has long been the source of irrefutable evidence that the aircraft went south after it disappeared from Malaysian military radar coverage, while accurate as far as what Inmarsat received is concerned, can be forged. This is what Jeff’s theory relies upon.
As I read through the New York Magazine article, I thought, “nah, Jeff’s just having fun and pulling our legs on this one.” Either that, or he’d gone bonkers. I mean, the bulldozed patch of land north of the airfield the size of a 777? Come on Jeff, it would be damn hard to tow the aircraft there from the airfield and not knock any buildings or get the plane stuck with a wheel leaving the asphalt. I began to remember the old discussions I had with Angela and found my mind reluctantly yielding to parts of Jeff’s theory. I thought, “If they landed there, they must have flown it elsewhere instead of burying the plane there.”
But to get to Baikonur, the BFO data would have to be faked. But then Jeff started to talk about the 3 ethnic Russians onboard with 2 from from Odessa in Ukraine, and one from Irtkusk. Then my mind started thinking.

Jeff toyed the mind with the following:
Could any of these men, I wondered, be special forces or covert operatives? As I looked at the few pictures available on the internet, they definitely struck me as the sort who might battle Liam Neeson in midair.
At first I was going to chuckle, but then Jeff mentioned where the 2 Ukrainians sat:

The alarm bells in my head suddenly went off. The 2 Ukrainians sat right under where the Satcom antenna would be , and on the side where the controller boxes would be located (left aisle). As coverage of these 3 people were at the end of his article, I immediately contacted Jeff.
I told Jeff that many of those claiming ruse operations claim that the whole BTO and Aircraft Earth Station (AES, the aircraft’s satcom system) identifiers were faked which is too outlandish in my opinion. Faking the BFO however, was a lot easier.
- The 3 people all had connections with wood. The Russian has a lumber company while the 2 Ukrainians had a furniture company. Coincidence?
- The Russian sat near to where the E/E bay would be, but I told Jeff that there was no need for anyone to enter the E/E bay, and definitely not on the initial stages.
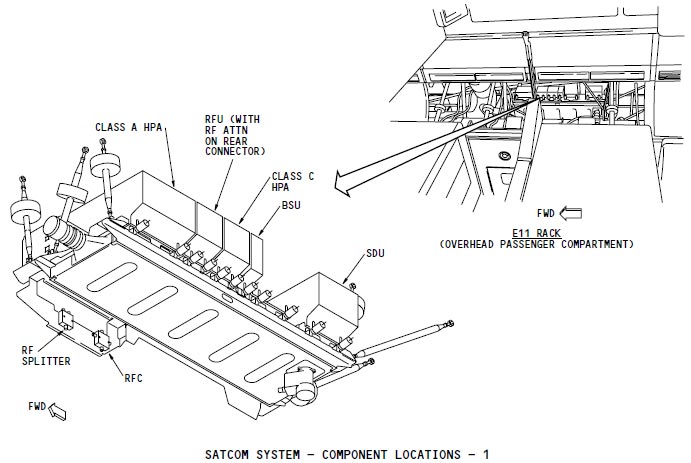
- The 2 Ukrainians sat just under and in front of where the access panels to the Satellite Data Unit would be above the cabin ceiling.
Obviously, Jeff was immediately hooked on this. So a small discussion between me and Jeff ensued.
In 2011, I led the Aerospace and Defence Solutions department at one of the local Inmarsat resellers here in Indonesia. I told him that back then I have heard rumours of 2 Indonesian guys who have managed to remote spoof the Doppler while they worked for Inmarsat during integrity testings of the Inmarsat 3 system. And then in several defence related meetings in 2011, I was also told that the other guys who can spoof the Doppler (remote or through the satcom terminal) are Israelis (using Russian immigrant engineers), the Chinese (using the Israeli expertise) and the Russians too, but obviously my sources didn’t want to go into details. The other interesting thing is that the Israelis do have their own set of satcom engineers dealing with “new innovations” for Inmarsat satcom, through one of the Inmarsat Distribution Partners, so, nothing surprising there if anyone can spoof the BFO… all you need to do is spoof the Doppler
How do you spoof the BFO?
The BFO is the error of the Doppler correction between the aircraft and the satellite, with the assumption that the satellite was static in orbit, while it is in fact moving in a small elliptical orbit around it’s geo-stationary point. The aircraft feeds it’s position and orientation to the satcom system, so that the Satellite Data Unit (SDU) can determine how much frequency adjustment is needed and where to point the antenna beam.
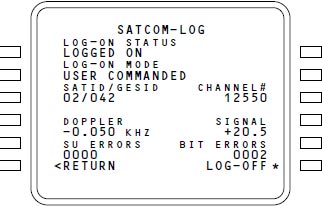
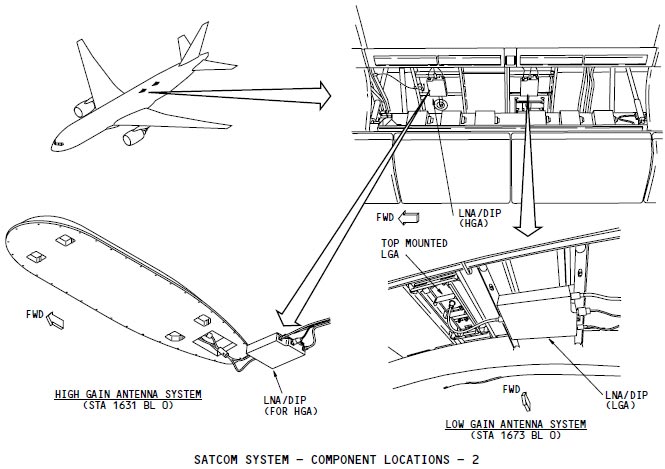
I can not discuss this deeper in public but one can replace the data feed from the aircraft system into the SDU. The aircraft’s Inertial Reference System(IRS) data to the SDU through an ARINC feed (standard physical and software interface), but these can be replaced by an independent Satellite Reference Unit (SRU) which is basically an IRS on an independent box. You can also have SRU or IRS feed ARINC emulators, based on discussions with some satcom systems manufacturers. These emulators can run on a laptop and that’s why my eyes jumped at the 2 Ukrainians sitting under the satcom system.
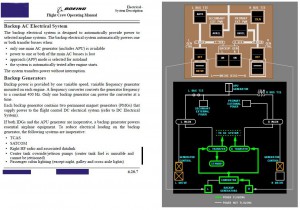
Take over the aircraft… then switch off the transponders… depower left main AC Bus, or pull the CB in the E/E bay… open the roof panel, take out the ARINC feed to the SDU, connect the spoofer, then repower when you need to. The 10,000ft logon, can be programmed into the SDU as far as I remember, so it doesn’t have to be the Satcom controller in the E/E bay or the FMC to do that.
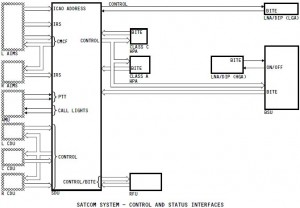
Some SDUs can be programmed to send positions as the aircraft passes certain altitudes (barometric or GPS depending on the desired source through the ARINC feed). A logon or a ping at 10,000ft can be programmed if one wants to, and that you can shut down the system through this emulator if you want. A more complex set up would be to manipulate the Doppler correction from the speed and position from the ARINC feed, then offset it through a processor, into the SDU.
All this is a LOT easier to do than to fake the unit identifier on a separate AES as what other “Fake satcom data” proponents have claimed. Jeff seemed overwhelmed in his reply.
You’re blowing my mind! I had no idea you’d gone down this path indendently — and cleary got further than I did. Can you access the SDU from the ceiling of the passenger cabin? I always figured they fed the faked IRS data from the E/E bay end of the ARINC cable. But it did seem odd to me that the Ukrainians were sitting under the AES.
I told Jeff that I got these information back in 2011 and had absolutely forgotten about them until I read his article about spoofing. It was only when I saw the 2 Ukrainians sitting below it did I remember all this!
During the discussions in great lengths with one of the satcom systems manufacturers about the various set ups, what I discovered was that many people know is the IRS data can be replaced with the SRU, or run it with a doppler correction emulator to replace the ARINC or SRU feed. The SDU has to be located near the High Power Amplifier (HPA) and Low Noise Amplifier (DLNA), so it is usually located above the cabin near the antenna. Can you access these boxes from the cabin? OF COURSE!
I was involved with a project on this for a fleet of A330s that were normally chartered by a head of state, and SatCom security was a concern that was raised by all parties involved, as the set up was to have someone sitting near and below the AES to activate the system and it’s security. So, reverse that, and see the 2 Ukrainians sitting where they sat and…
Of course, the 2 didn’t sit exactly under where the SDU rack would be, but pretty near it. And remember that in such a scenario, to control the cabin you do not need firearms. Scary? Of course! Jeff’s reaction to this was blunt and clear.
Holy crap!
If this is true then what happened?
Assuming that something like this happened, my chain of events still differ from Jeff’s. The timing could be simple. An airband receiver can still receive what the aircraft transmitted on VHF, and you can get the aircraft’s accurate position through portable GPS, like the ones shown below:

Connect the GPS above to a display unit or a computer, and you can figure out where you’re at in the airspace, which airway you’re at, and therefore with an airband radio, figure out when to prepare and when to pounce at the cockpit during an ATC hand-off. Of course, how to enter the cockpit is a different story altogether and even if I know, I wouldn’t say it here.
After taking over the aircraft, the perpetrators had around 1 hour to set up the spoof. Assuming that we’re talking about a Russian backed heist, one can easily get “training” on the Satcom set up of a 777 in Russia (Aeroflot and Transaero operate 777s with fitted with the Inmarsat-3 system), and heck, even I could get some of the above information. First thing’s first, you need to switch off the satcom, and there are 2 ways of doing this.
Alternative 1: Get into the E/E Bay, or the main avionics bay below the front galley (which others have exposed the easy access as a security threat), and pull the circuit breaker on the right panel.
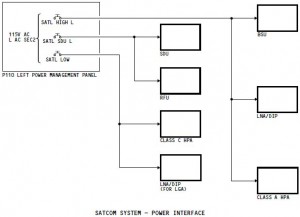
Alternative 2: Remove power from the Left Main AC Bus, and kill the TCAS, and most of the cabin lighting, in addition to removing power from the Satcom system. This can be done by isolating the Left Main Bus Tie and switching off the Left Generator.
After power has been removed from the Satcom system, the dirty deed could continue. Take out the feed cable, run it through a processor before re-feeding into the SDU; or, replace the whole feed with a processed feed using an SRU and a GPS, through a laptop. Either of these methods will enable you to provide various Doppler corrections in order to spoof the BFO data. One other way is just to run it through a frequency override made by let’s say the laptop, and allow the IRS feed to provide the position data.
Of course, take out the wiring etc, and then put it back on again with the hacked layout will take time. Whether 1 hour is enough or not, that’s the unknown, but if successful, one can log off and log on again at will, which can create the different log on hand shakes what has so far baffled us as to “Why?”
Wiring aside, is Satcom that vulnerable?
We rely more and more on high bandwidth satcom, and the Inmarsat system is the prevalent one out there. One can say that the idea of someone breaking into the overhead panels and fiddle with the satcom control boxes, is just ridiculous, but have a look at this set up at another Malaysian registered aircraft… you don’t need to open up cabin ceilings with this one!

Conclusions
Many will ask what’s the point if this article because it is obvious that I write this not to make people believe in conspiracy theories, and I also doubt that Jeff wrote his to get people to believe his conspiracy theory. However, what Jeff and I wrote, should raise some alarm bells with regards to safety and security.
Anyone who’s convinced that the 777-sized bulldozed ground at Baikonur is the burial place of MH370 should get their heads checked. If the aircraft did land there, it would have just been refuelled, and the satcom deactivated, and remained off as the aircraft took off again into real oblivion with the purpose of the spoof done, that is to misguide people elsewhere (like the southern Indian Ocean). But, do I think the airplane went north? No, not really. Both Jeff and I believe that the search on the southern Indian Ocean need to continue.
Due to MH370, ICAO is now considering making aircraft tracking via satcom as mandatory. Many are proponents of getting the tracking done by existing on-board satcom systems. However, I personally think that such a method is no additional means of security as we can see in this article that the current set up is nowhere near secure. The SDU and HPAs are where they are because they physically NEED to be close to the antenna to ensure good quality signals.
Mandatory tracking should be done through a less expensive system that can be applied universally, that is separate from the passenger satcom systems and/or cannot be tampered with in flight. The current set up installed on many aircraft as shown, isn’t tamper proof. The last thing we need is for someone to be able to tamper with the tracking portion by accessing the physical boxes of the satcom controls and spoofing or hacking into the Satellite Data Unit, or even, destroying it, as gaining access to them is pretty easy.
Current Inmarsat-4 (Swift Broadband) antennas have their own embedded GPS that can be used for tracking by taking the data and transmitting it through as customer payload, or through the non-payload data packets. The latter would be more secure, so far, for those who wants to not add anymore hardware onto aircraft installed with these systems.
This article is to raise alarms beyond flight safety and security, but also touches on data security of on-board air-to-ground data communications used by the passenger. Those in the industry should know what I mean and why details aren’t divulged in this article… it would be just too damned tempting to be abused by the bad guys, but the current set up can easily result in abuses of privacy and mining of personal data.
The fact is, security wise, on-board internet security is still poor. We had a provider of on-board internet spoofing SSL security certificates recently, which can compromise private data such as access passwords and e-banking security. Wanting to use these systems as is for safety purposes, can and probably will open up a can of worms.
As this article shows, from the crypto-investigation “hobby” of me, Jeff and many others, sleuthing through technical details, evidence, etc, can, when combined with a little imagination and analytical thinking, expose various risks we didn’t see before (even if it stared us right in the face).

nobody ever think about satcom security, even in presidential aircraft 😀
btw, cobham now made integrated antenna which moved all the electronic equipment in the radome, leaving no equipment inside pressure fuselage. this approach provides more secure, tamper-proof system, but also have a drawback: raise the maintenance cost & complexity.
Gary instead of trying to find the most complex solution, try to find the simplest one.
If MH370 did suffer depressurisation at 35,000ft then all the avionics were subjected to intense cold around -53 degrees centigrade.
When you freeze metal the electrical resistance reduces. That means electrical signals pass through metal more quickly. If that happened on MH370 then the signal path delay was reduced.
If the signal path delay was reduced then the BTO values shrunk west towards the satellite.
The offset error could be 300-400 nautical miles. This would mean the real 7th Arc is greater distance from the satellite.
It also means if decompression happened before 18:25 UTC then MH370 did not turn south near Sumatra but flew south from Vietnam.
Regards
Simon Gunson
New Zealand
Simon,
The point of the article is not to find the plane, nor is it to advocate that the airplane is not in the southern Indian Ocean. The official data used shows the aircraft overflying Penang then turned northwest, this is what makes it difficult because then the BFO data shows it went south, and therefore the probable trajectory has to fit the southern scenario for the BTOs.
The article I wrote anyway is to expose the security risks we have. That’s all it is.
Regards,
Gerry
Gerry,
Thank you for this thoughtprovoking and detailed article.
I have one question, though: You wrote that you knew as early as 2011 about certain factions who might’ve tried to spoof BFOs. Why would they do this? Inmarsat’s calculations only pointed to a Southern route, because their satellite wasn’t geostationary anymore, but their compensation algorithms treated it as still being geostationary. But that woulld not be the case with all satellites , no? So what would be the benefits of being able to spoof or distort the BFOs? Would there also be a benefit if hypothetical perpetrators had to deal with a truly geostationary satellite?
Sabine,
One does not spoof the BFO per se, but one can cause the doppler correction for the transmissions. There are many (devious) uses to spoofing the doppler. In Mobile Satellite Services, the doppler correction on fast moving earth stations (antennas on aircraft) is needed, and the station keeping of the satellite needs to be within certain tolerances of movements when in “geostationary” orbit. Inmarsat 3 was not at the outset designed for aeronautical MSS, but was made capable for it. To allow for a certain “wobble orbit” so to speak, can save a lot of fuel for the satellite station keeping.
If the station was truly geostationary, the Doppler spoofing can still be useful for those with devious intentions, because one cannot know where along the ping ring one would be, and spoofing the closure rate (doppler), when under a long time interval between contacts, can create confusion to those trying to find where the transmissions were made from.
The point of the article is not to say that MH370 BFOs were spoofed, but how easy it is to gain access to the SDUs, and add a little doppler shift manipulation possibilities… They need to mitigate this security risk.
Thanks Gerry,
You answered my question why a potential perpetrator might try to explore the possibility of spoofing the doppler – no matter if a satellite was allowed to develop a slightly “wobbly” orbit or if it was truly geostationary.
I fully understand that the purpose of your article was to point out aviation security issues and that you didn’t intend at all to imply that something like this happened aboard mh370. But your technical insight is fascinating and slightly disturbing nevertheless.
Sabine, it disturbs me a lot… to the extent of me saying it on the intl media.
Gerry I am aware the official version is that MH370 flew low over Penang and indeed even reference to the co-pilot’s cell phone making contact with a cell tower on Penang.
Not that I believe this cell contact happened, but for that to happen MH370 would have to fly below 5,000ft even just to establish a fleeting connection and pass no further than 30km from the tower.
Work this through… At 5,000ft a Boeing 777 can only manage a True Airspeed of 350 knots.
To fly from IGARI at 17:21 UTC to Pelau Perak at 18:02 UTC requires a True Airspeed of 430 knots. Because of air density MH370 could not achieve this speed below 18,000ft where it would have clearly been seen by several primary radars.
Gerry regardless of the point of your article you do not address the point I have made. The BFO track only has relevance so long as you can measure it from a verifiable position.
For the benefit of the search effort they assumed this verifiable position to be a radar sighting at MEKAR at 18:22 UTC.
I do not accept this radar sighting was genuine. Equally capable military PSR radar at Lhokseumwae was looking at the same airspace and saw nothing. How do you account for this?
RMAF chief General Rodzali Daud first denied any radar sighting of MH370 over the Straits in the first week of MH370’s disappearance. Then General Daud issued a press statement on 11 March 2014 confirming that military radar at Butterworth (as he said it) saw MH370 fly from IGARI to VAMPI-GIVAL_IGREX and pass by Pelau Perak at 18:40 UTC.
Malaysian officials have issued so much false and conflicting information about an alleged flight through the Straits that I am saying to you that none of the official version is credible.
The BTO values being altered by decompression is something which i am asking you to respond to. It means that all the BTO Arcs after 17:07 UTC are unreliable and appear to have been shifted (contracted) west.
That is what spoofed the data. Not deliberate tampering, but an inability by “EXPERTS” to consider or even understand the impact Decompression would have in disrupting their BTO calculations.
I was addressing the issue of “spoofing” data which was raised in your article.
The interim report made yesterday made no reference to low level flight over Penang, and that the lowest the airplane went after the turnback while still under primary radar coverage, was 31,100 ft if I remember correctly. And I for one, never subscribed or even consider the low level flight theory as plausible once the last ping time was announced… And yes, down to 5000ft and meet the “deadlines”, was physically impossible. 🙂
Simon,
If you do not believe that none of these radar sightings are genuine then you have nothing to go on as to what happened to the aircraft.
The PSR at Lhokseumawe might have been switched on, or off… we just do not know. Besides, the Indonesian authorities have stated that our radars did not see MH370 over our territory. This means just that. If we saw MH370 outside our territory, then we haven’t lied.
If you’re saying that the information of BTOs and BFOs are screwed because of decompression, my answer is, so what? I am not discussing that on this page, and it is irrelevant to the underlying reason why I wrote this article, therefore , I do not have to address the point you have made, nor respond to your demands on this site. Why are you making demands anyway? What right do you have in imposing your demands on me and/or this site?
Feel free to raise this issue again should I write an article that discusses the intricacies of BTOs (to which replying is also subject to my discretion).